Is Facial Recognition Technology a Threat to Privacy? 1 Shocking Truth
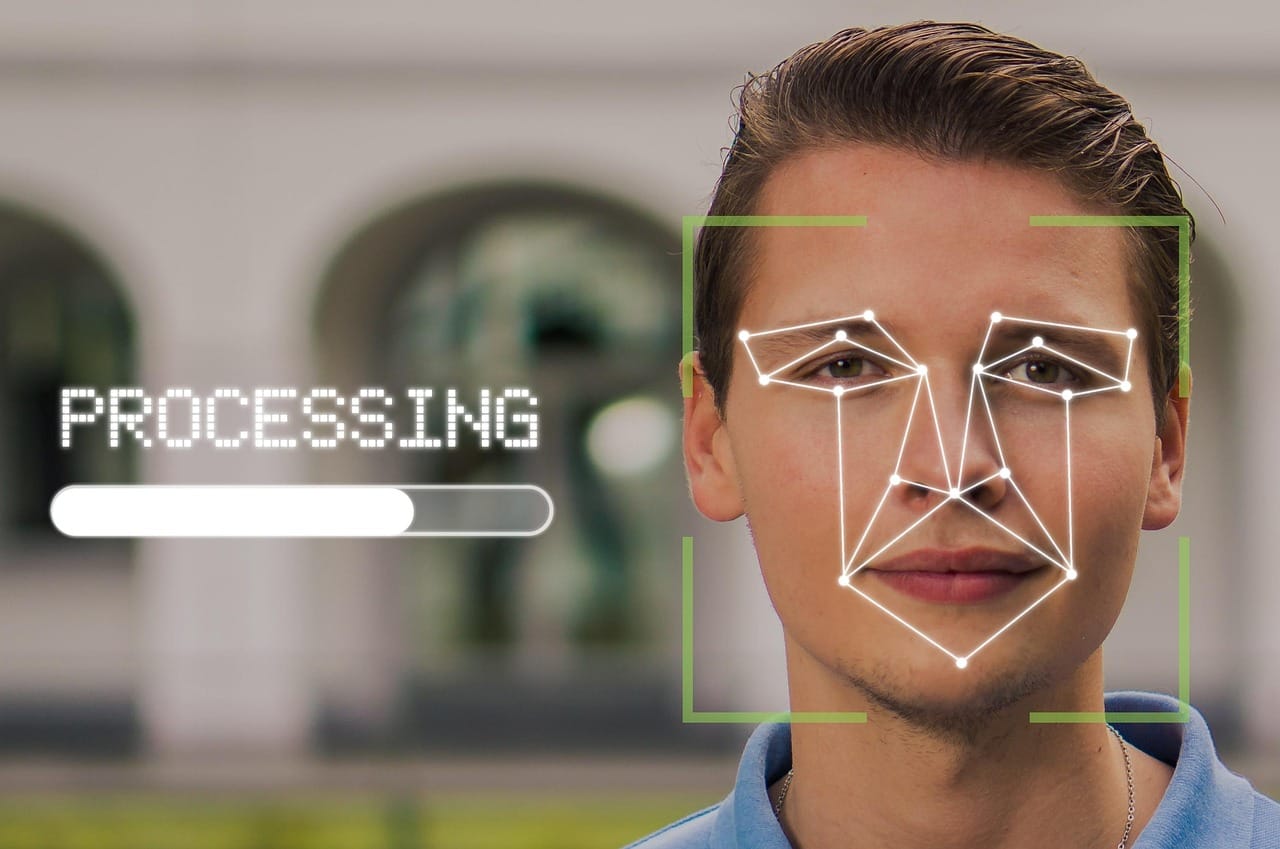
Is Facial Recognition Technology a Threat to Privacy… Did you know that by 2024, facial recognition technology is expected to be used in over 97% of smartphones worldwide? As this powerful technology becomes increasingly ubiquitous, it raises a chilling question: Are our faces becoming the new fingerprints of surveillance? While proponents tout its benefits for security and convenience, critics argue that it poses an unprecedented threat to our privacy, enabling constant monitoring and data collection without consent. As we delve into the implications of this rapidly advancing technology, we must confront the stark reality: is facial recognition a safeguard or a serious invasion of our personal freedoms?
Is Facial Recognition Technology a Threat to Privacy?In the age of rapid technological advancement, facial recognition technology (FRT) has emerged as one of the most talked-about innovations. It promises convenience and security but also raises significant concerns regarding privacy. So, is facial recognition technology a friend or foe to our privacy? Let’s dive into the discussion!
Understanding Facial Recognition TechnologyFacial recognition technology uses algorithms and artificial intelligence to identify or verify a person’s identity based on their facial features. Here’s how it generally works:
While the potential risks are significant, FRT also comes with several advantages. Here are some benefits that proponents often cite:
On the flip side, the implications of FRT on privacy are alarming. Here’s where it gets controversial:
To better understand the debate surrounding facial recognition technology, let’s take a look at the contrasting viewpoints in the following table.
| Aspect | Proponents | Opponents | |
| Privacy | Can enhance personal safety | Erodes personal privacy | |
| Security | Aids in crime prevention | Can lead to wrongful arrests | |
| Accuracy | Improves with technological advancements | Still prone to errors and biases | |
| Consent | Can be used with user consent | Often implemented without public knowledge | |
| Regulation | Support for industry self-regulation | Calls for strict government legislation |
The ethical implications of FRT are profound. Many countries are grappling with how to regulate its use. Here are some key points often discussed:
Facial recognition technology is a double-edged sword. While it offers convenience and security, it also poses significant risks to privacy. The challenge lies in finding a balance that maximizes the benefits while minimizing the drawbacks.
As society continues to navigate the implications of this technology, it is crucial for individuals, businesses, and governments to engage in thoughtful discussions about privacy rights, ethical considerations, and the future of technological innovation. Whether FRT becomes a trusted tool or a pervasive threat to privacy will largely depend on the decisions we make today.
So, what’s your take? Is facial recognition technology more a friend or foe? Let’s keep the conversation going!
In conclusion, while facial recognition technology offers significant benefits in areas such as security and convenience, it also raises substantial concerns regarding privacy and the potential for misuse. The balance between leveraging this powerful tool and protecting individual rights is a critical issue that society must navigate. As we move forward, it’s essential to consider how we can establish regulations that safeguard privacy without stifling innovation. What are your thoughts on the implications of facial recognition technology for our privacy rights?
Why Your Face Is Different From a Password
Passwords are replaceable. Faces aren’t. That single fact changes the privacy calculus more than most people realize. If a password leaks, you rotate it. If your faceprint leaks-whether it’s a template derived from your facial geometry or a set of embeddings produced by a model-you can’t rotate your face. You can grow a beard, change your hair, or wear glasses, but biometric systems are built to handle those changes. The point of the technology is persistence.
That persistence creates a unique kind of privacy risk: biometric data can become a lifelong identifier that follows you across time, platforms, and physical locations. Even if a company promises it will only use facial recognition for “security,” the existence of a stable identifier makes secondary uses tempting-especially when incentives shift.
The Data Pipeline: Where Privacy Is Actually Lost
To assess whether facial recognition is a threat to privacy, you have to look beyond the camera. The privacy impact is determined by the entire pipeline: capture, processing, storage, sharing, and retention.
1) Capture
Capture can be obvious (you opt into face unlock) or ambient (cameras in public spaces, doorbells, retail stores, workplace entrances). The ethical difference is consent: in many environments, you are captured simply by being present.
2) Processing
Processing includes face detection (finding a face in an image), face analysis (estimating attributes), and face recognition (matching to an identity). Even if a system claims it is “not doing recognition,” detection and analysis can still produce privacy-invasive outcomes like tracking movement patterns or inferring traits.
3) Storage and Retention
Some systems store raw images, some store templates, and some store both. Retention policies matter more than marketing. If face templates persist indefinitely, they become a durable surveillance asset. If they’re deleted quickly and can’t be reconstructed, risk drops significantly.
4) Sharing and Linking
Risk spikes when data is shared across vendors, affiliates, or government agencies, or when it’s linked to other identifiers like phone numbers, loyalty accounts, device IDs, or location histories. Linking turns a face match into a rich profile.
Is Facial Recognition Technology a Threat to Privacy When It’s “On Your Phone”?
Phone-based facial recognition is often presented as the benign version: it’s personal, local, and user-controlled. Sometimes that’s substantially true, but it depends on implementation and ecosystem behavior.
The privacy-friendly scenario looks like this: your face data is enrolled locally, converted into a template stored in secure hardware, and used only for on-device authentication. No raw face images are uploaded, and the template can’t be extracted in a usable form. In that model, the threat is mostly limited to device theft, coercion, or poor recovery controls.
The privacy-risk scenario looks different: face data is used to power cloud features (photo tagging, “memories,” cross-device identity), or face embeddings are used to improve models and analytics. Even if the system is secure, it normalizes the idea that face-derived identifiers are just another data point to collect and optimize.
In other words, “it’s on your phone” can be privacy-protective, but it can also be the gateway that makes face recognition socially acceptable everywhere else.
Mass Surveillance vs. Point Security: The Same Tool, Different Ethics
Facial recognition is ethically ambiguous because it can be deployed in two fundamentally different ways.
- Point security: verifying identity in a narrow context (unlocking a device, accessing a secure workplace area) with explicit consent and strict retention.
- Mass surveillance: identifying or tracking people across large populations, often without meaningful consent and with broad retention and sharing.
The problem is not just what the tool can do, but what governance allows it to do. Without strong constraints, point security deployments can quietly expand into mass surveillance through “function creep”: a system installed for one purpose becomes valuable for others, especially when it starts producing actionable intelligence.
Function Creep: How “Safety” Becomes Tracking
Function creep is the most predictable pathway from convenience to intrusion. It typically follows a pattern:
- Limited adoption: a system is justified by a narrow security need.
- Infrastructure buildout: cameras, databases, and vendor contracts become sunk costs.
- Expansion of use cases: “If it can stop fraud, it can stop shoplifting. If it can stop shoplifting, it can flag suspicious behavior. If it can flag suspicious behavior, it can identify people of interest.”
- Normalization: people stop noticing because the system becomes background.
Once normalized, reversing the deployment becomes politically and economically difficult, even if the public later objects. That’s why the most important privacy decisions often happen early-before systems are ubiquitous.
Accuracy Is a Privacy Issue, Not Just a Technical One
Inaccuracy isn’t only a fairness problem; it’s a privacy problem because it increases the odds that your identity will be incorrectly assigned, stored, shared, and acted on. A false match can create a persistent record that follows you across systems, especially when databases are reused and error correction is slow.
Misidentification also interacts with incentives. If a system is used for law enforcement, workplace security, or retail loss prevention, the harm of a false match isn’t theoretical. It can lead to escalations that are hard to undo. Privacy is partly about controlling where you appear in records. False matches steal that control.
The “Consent” Problem in Public Spaces
Consent works poorly in physical environments. In an app, you can opt out (at least in theory). In a train station, mall, or street, opting out may require leaving the space entirely. That’s not meaningful consent; it’s coerced participation through social necessity.
This is where facial recognition becomes uniquely invasive compared to other identifiers. You can leave your phone at home. You can pay cash. But you can’t leave your face behind. If public spaces become face-scanned by default, anonymity in public-a foundational social freedom-can quietly disappear.
Comparisons: Faceprints vs. Fingerprints vs. Location Data
It’s tempting to say, “We already use fingerprints, so what’s the difference?” The difference is scope and capture friction.
Fingerprints typically require deliberate contact and controlled enrollment. Location data can be invasive, but it’s often mediated through devices and permissions. Facial recognition can be passive, ambient, and scalable in a way that makes it ideal for broad identification without interaction.
That passivity is the privacy threat: the system can identify you when you’re not “doing” anything-just existing in a camera’s field of view. As camera networks expand, the identification surface expands with them.
What Strong Privacy Safeguards Actually Look Like
Not all facial recognition deployments are equally dangerous. The difference is governance, architecture, and enforceable limits. Strong safeguards share common features:
- Purpose limitation: explicit, narrow use cases with bans on secondary uses.
- Data minimization: store the minimum necessary; avoid raw image retention.
- Short retention: automatic deletion timelines that are technically enforced, not optional.
- Local processing when possible: keep recognition on-device or on-premises with strict access controls.
- Access logging and audits: every query should be logged, reviewable, and attributable.
- High thresholds for action: recognition results should be treated as leads, not proof, especially in punitive contexts.
- User rights: clear ways to access, challenge, and delete data where applicable.
The key idea is that privacy protection must be structural. Relying on promises is not a safeguard; it’s branding.
Practical Steps Individuals Can Take Today
Individuals can’t fully solve systemic surveillance, but you can reduce exposure and improve control in everyday life.
- Audit face features: review photo tagging and face grouping settings in your major photo platforms.
- Limit cross-platform identity: avoid linking your real identity to every service, especially retail and loyalty ecosystems.
- Harden accounts: strong authentication reduces the chance your face-related data becomes accessible through account takeover.
- Be selective with opt-ins: enroll face unlock on devices you physically control and understand; avoid unnecessary third-party face services.
- Push for transparency: in workplaces, schools, and buildings, ask what is collected, who has access, and how long it’s retained.
These steps won’t eliminate facial recognition in public spaces, but they reduce the volume of face-linked identity trails you create voluntarily.
Where the Debate Lands: Safeguard or Invasion?
Facial recognition can be a safeguard in tightly controlled, consent-driven contexts with strict retention and strong technical protections. It becomes a serious invasion when deployed at scale without meaningful consent, when data is retained or shared broadly, or when it is used to create continuous identification in public life.
The most honest answer is conditional: the technology itself is not destiny, but its default incentives lean toward expansion. Convenience and security arguments make adoption easy. Privacy protection requires explicit friction-rules, audits, limits, and consequences for misuse. Without those, faces do risk becoming the new universal identifier for surveillance.
FAQ
Is facial recognition the same as face detection?
No. Face detection finds that a face exists in an image. Facial recognition attempts to match that face to an identity or a known template. Detection can still be invasive when used for tracking patterns, but recognition increases the privacy stakes dramatically.
Does using facial recognition to unlock my phone threaten my privacy?
It can be relatively privacy-friendly if the biometric template stays on-device in secure hardware and is not uploaded. Risks increase when face data is used for cloud features, cross-device identity, or broad analytics.
Why is facial recognition in public spaces considered especially risky?
Because consent is weak and capture is passive. You can’t meaningfully opt out without avoiding the space, and identification can happen continuously without interaction.
Can facial recognition be accurate and still harmful?
Yes. Even perfectly accurate recognition can enable mass tracking, chilling effects on speech and association, and the creation of permanent identity trails. Accuracy doesn’t solve surveillance.
What policies reduce privacy harms the most?
Clear purpose limitation, strict retention limits, bans on secondary use, strong audit requirements, and restrictions on mass surveillance deployments. The most important safeguards are enforceable constraints, not voluntary guidelines.
How can I reduce my exposure to facial recognition?
Limit opt-ins for face-tagging features, avoid linking identities across services, secure your accounts, and ask for transparency in places that deploy recognition. You can’t control every camera, but you can reduce the face-linked profiles you generate voluntarily.
Should facial recognition be banned entirely?
Reasonable people disagree. A narrow ban on mass surveillance use is easier to justify than banning all uses, including consent-based point security. The core question is whether safeguards can be made strong enough to prevent function creep and abuse.
Ultimately, the privacy threat isn’t just identification-it’s normalization. Once constant face-scanning feels routine, people self-censor, avoid gatherings, and accept profiling as “modern life.” That subtle behavioral shift can quietly shrink freedom long before any law changes.

